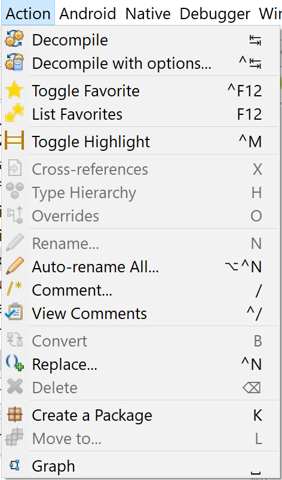
Actions
The primary use case for JEB is the analysis of binary code. This section focuses on the basics of code analysis and refactoring:
- Renaming items such as methods or fields
- Changing the code structure by moving items to packages
- Commenting
- Navigating a code base via cross-references
- Viewing type hierarchies
- Viewing method overrides
- Graphing routines (CFG)
- Replacing items or rebasing immediates
- Auto-renaming all items
In the GUI client, many fundamental interactions can be achieved via the Action and Navigation menus. Those actions are implemented by most JEB analysis modules that perform code disassembly.
Other action groups such as Native code actions and Debugging actions are detailed in separate sections of this manual.
Warning
The examples in this section are based on the analysis of a sample Android app using the Android Dex parser. Keep in mind that features and behaviors of Actions depend on the module implementing and performing them.
Decompiling#
The next section covers decompiling code in depth.
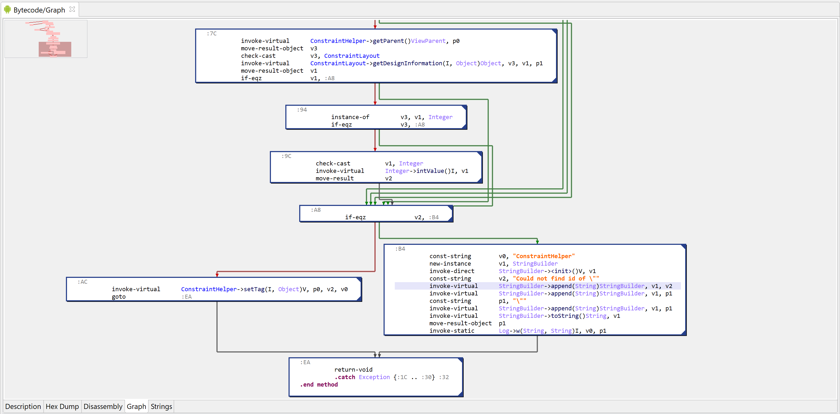
Graphing#
Users can alternate between the default interactive full disassembly view and the interactive control flow graph of the currently examined method/routine.
Press the Space key to go back and forth. In some circumstances, users may prefer graph navigation.
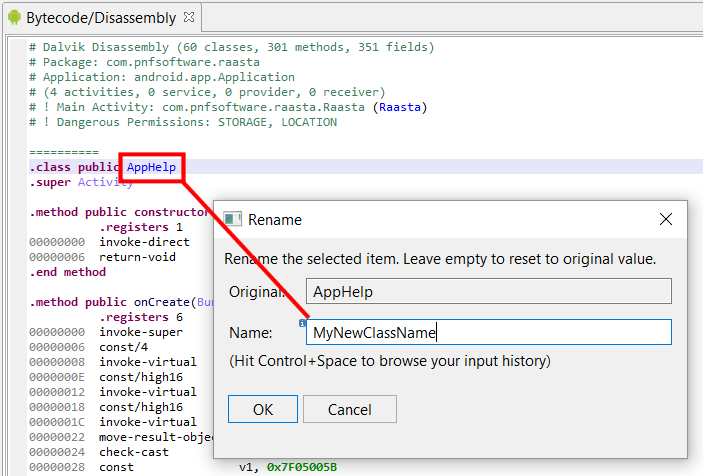
Renaming#
An important requirement for analysts is the ability to rename code items such as types, methods and routines, fields and data items, packages, etc. consistently across a code base.
- Position the caret on the item to be renamed
- Hit the N key or select Action, Rename
- Enter the new name and press Enter
Tip
Within the Rename dialog box, press Ctrl+Space (Command+Space on macOS) to bring up your renaming history.
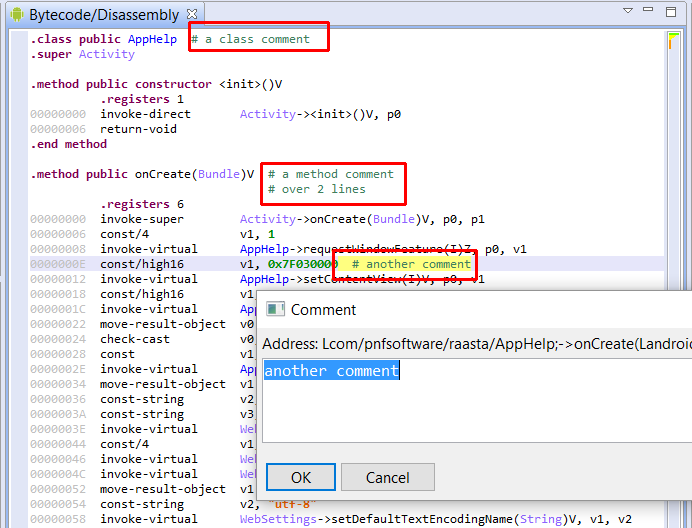
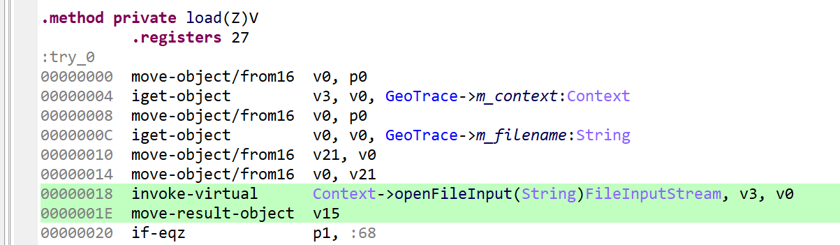
Commenting#
When in a code view, press the / (slash) key to add a comment.
Warning
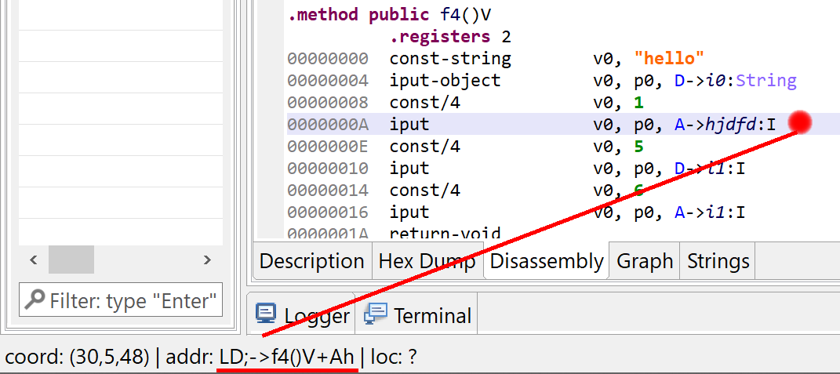
Comments are attached to addresses or items, therefore make sure to be on a valid address - else no comment can be attached. The caret address is always displayed in the status bar:
Navigating#
Pressing the Enter key on an item or double-clicking it will bring the caret to the definition of the item.
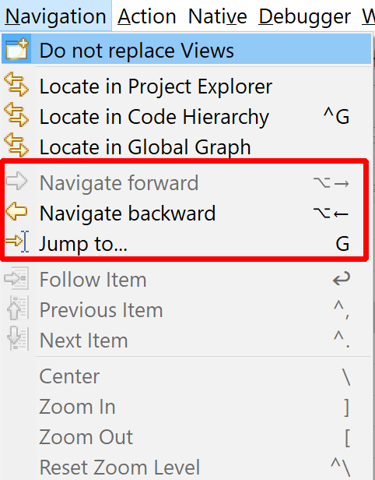
You can navigate backward and forward using the traditional Alt + Arrow Left (or Escape) and Alt + Arrow Right key combos, or via the Navigation menu.
The Next Item and Previous Item command allow you to jump to the similar item after or before the currently selected item.
Cross-references#
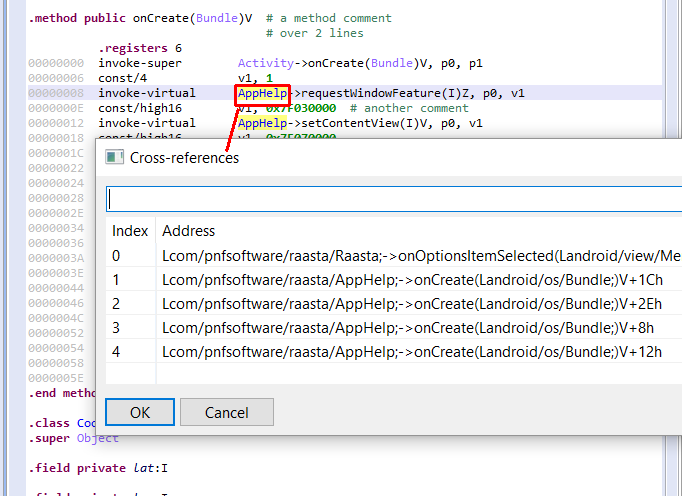
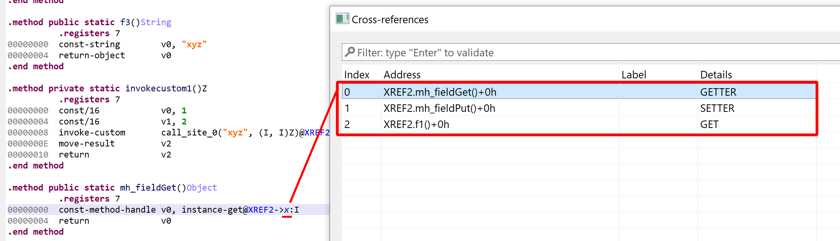
Cross-references on an item allow the examination of items referencing it. Press the X key to visualize them.
You can jump to a cross-reference by double-clicking it.
The cross-reference dialog generally includes additional information attached to the referenced location. That information is plugin-dependent. Below, the Details column provides the kind of reference (on a field item, in that case), e.g. a GET (read), or something else.
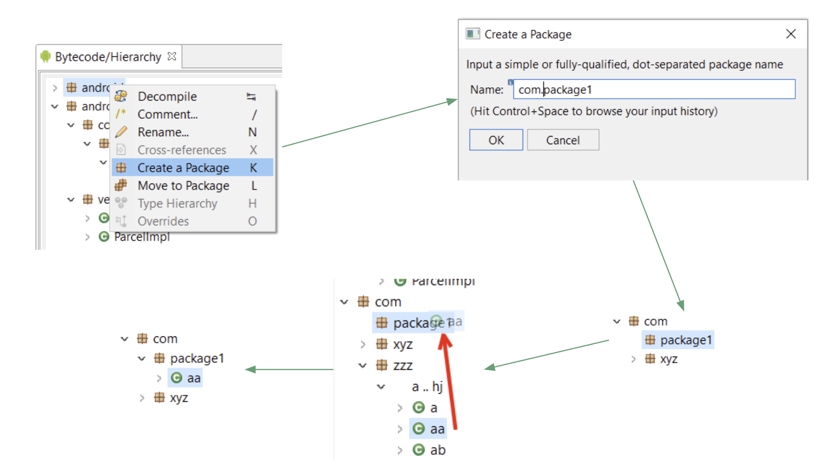
Restructuring#
The Create Package and Move to Package actions offer powerful refactoring possibilities, especially useful in the case of large obfuscated binary files.
If the module supports it, users are able to:
- Create artificial packages (aka, namespaces) using the K key.
- Move items, such as types, to existing or artificial packages using the L key.
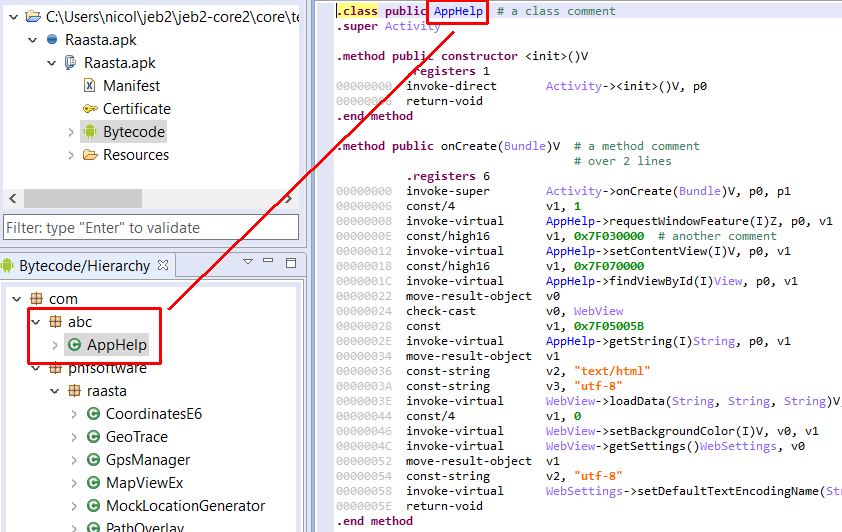
The following screenshot is an example where the class AppHelp was moved from the com.pnfsoftware.raasta package to a newly created package named com.abc.
Note
Have a look at our YouTube demo video that demonstrates advanced refactoring and automatic restructuring of a heavily obfuscated Android malware application.
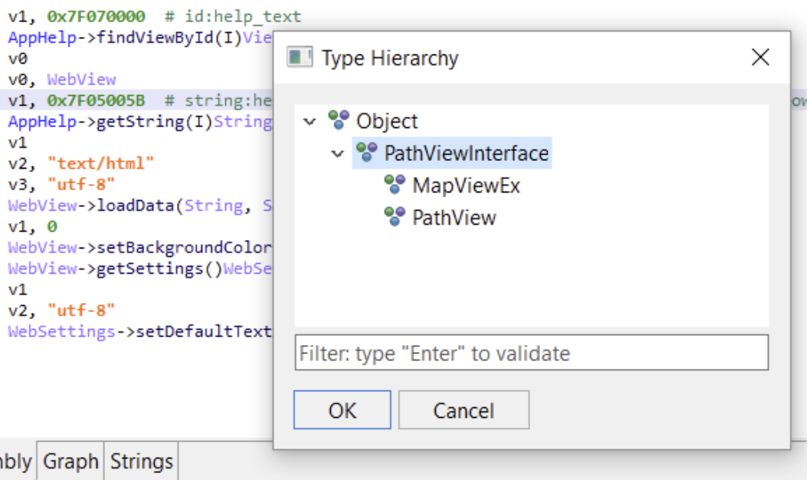
Type Hierarchies#
The H key allows the examination of type hierarchy, such as parent classes, descendant classes, implemented interfaces, etc.
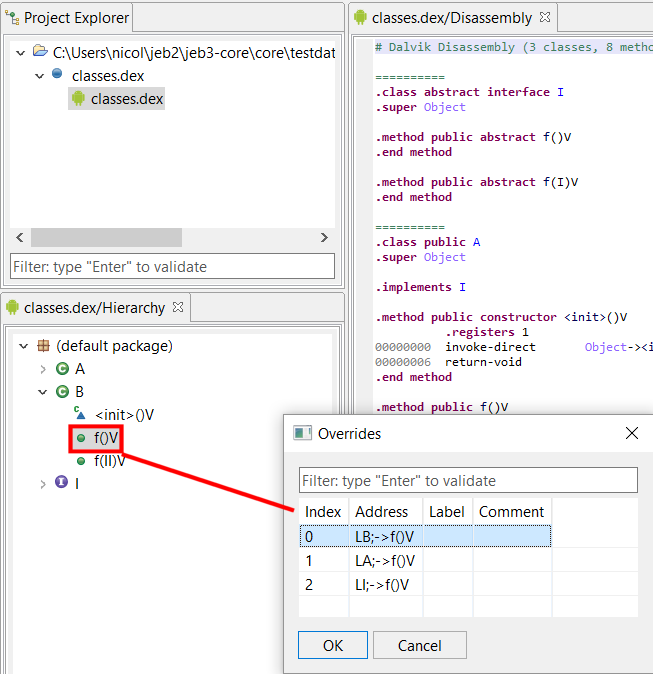
Object Overrides#
The O key allows the examination of overrides, such as virtual method redefinitions in the case of object-oriented bytecode files.
Rebasing Constants#
This feature allows the selection of the radix used to render immediate constant integers. Press the B key repeatedly to cycle through the bases offered by the plugin.
Typically, bases 8, 10, 16 are offered. Some plugins may offer additional bases such as base 2, or non-conventional representation modes, such as character-based immediate rendering.
Auto-Rename All#
This action may be offered by plugins to allow blanket renaming of all items to automatically-generated names.
Note
The Dex plugin provides this option to auto-rename types, fields, and methods to better names if they have been obfuscated to unreadable or compressed strings. Have a look at the Android section to learn more.
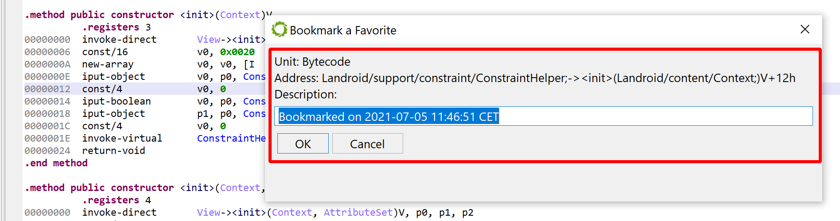
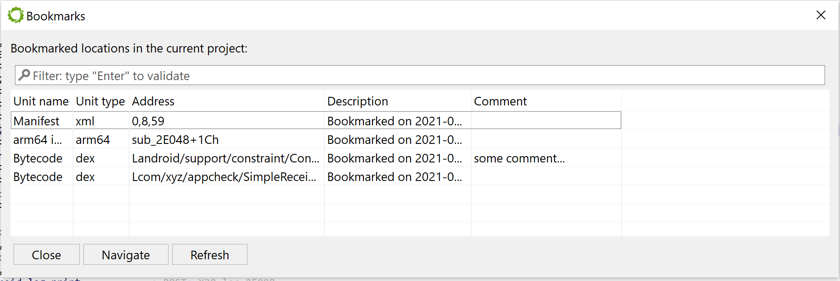
Favorites#
You may bookmark favorite locations and quickly retrieve positioned favorites using the Action menu.
The Favorites dialog (F12 by default) shows all favorites in your project. Navigate to a positioned favorite by double-clicking on a row. The dialog is modeless (it can stay open while you work on the project).
To remove a bookmark: go on the bookmark location; edit the bookmark; set the new bookmark to an empty string. The bookmark will be discarded.
Like everything else, the bookmarks can also be accessed and managed programmatically: refer to IRuntimeProject.getBookmarkManager().
Highlights#
Lines in interactive text views, such as disassembly or decompiled views, can be highlighted using the Action, Toggle Highlight (Control/Command + M by default).