JEB
JEB is our reverse-engineering platform to perform disassembly, decompilation, debugging, and analysis of code and document files, manually or as part of an analysis pipeline.
Android Decompiler + Android Debuggers
Use JEB to perform reverse engineering of malicious APKs and security audits.
Cut down on costly reverse engineering time: decompile obfuscated APKs, examine Java code and debug closed-source apps in minutes. Our modular back-end, coupled with a powerful UI front-end for desktop platforms, allow refactoring operation and scripting to automate complex tasks.
Perform static and dynamic analysis of Android applications, goodware or badware, small or large.
- Decompile code using our Dalvik decompiler, including multi-dex APK.
- Refactor the analysis to defeat obfuscated code generated by application protectors.
- Reconstruct resources and obfuscated XML files.
- Debug Dalvik code as well as all native code (Intel, ARM), seamlessly.
- Automate and script your reverse engineering tasks via our API.
Powerful
Perform precise and robust decompilation of Android apps and Dalvik bytecode.
Our in-house decompiler includes optimizers able to auto-decrypt contents, unreflect API calls, and clean-up many types of obfuscated code.
Our Dalvik and native code debuggers offer features to seamlessly analyze real-time apps, allowing examination of code and hooking of sensitive APIs.
Flexible
Refactor, annotate, navigate, and modify the analysis output.
Our analysis modules support code refactoring, virtual hierarchy to organize highly obfuscated code, or code cleaning (for instance when decrypting obfuscated contents or un-reflecting code).
Extensible
Leverage the JEB API to automate reverse engineering tasks.
Using Java or Python, users can write scripts and plugins to automate the reverse engineering process. Power users can write full-blown analysis modules and headless front-ends. Decompiler extensions accept user-provided IR optimizers to further clean up obfuscated code.
Intel x86 Decompiler
Use JEB to reverse engineer x86 32-bit and x86 64-bit programs and malware.
The x86 decompiler and x86-64 decompiler provide the following features:
- Augmented disassembly including resolution of dynamic callsites, candidate values determination for registers, dynamic cross-references, etc.
- Decompilation of x86 and x86-64 to pseudo-C source code.
- Partial Class Recovery and Decompilation to C++ for programs compiled with MS VCPP (see video).
- Advanced optimization passes to thwart protected or obfuscated code.
- Win32 type libraries and common signatures for efficient Windows file analysis.
- Interactive layer allowing refactoring: type definition, stackframe building, renaming/commenting/cross-referencing, etc.
- Full API and access to the Intermediate Representations to perform advanced and/or automated code analysis in Python or Java.
ARM Decompiler
Use JEB to reverse engineer programs and malware written for ARM platforms.
Our ARM machine code decompiler allows reverse engineers and security auditors to analyze malicious ARM binary files.
The ARM decompiler provides the following features:
- Augmented disassembly including resolution of dynamic callsites and syscalls, candidate values determination for registers, dynamic cross-references, etc.
- Decompilation of ARM 32-bit and ARM-Thumb code to pseudo-C source code.
- Advanced optimization passes to thwart protected or obfuscated code.
- Interactive layer allowing refactoring: type definition, stackframe building, renaming/commenting/cross-referencing, etc.
- Full API to perform advanced and/or automated code analysis in Python or Java.
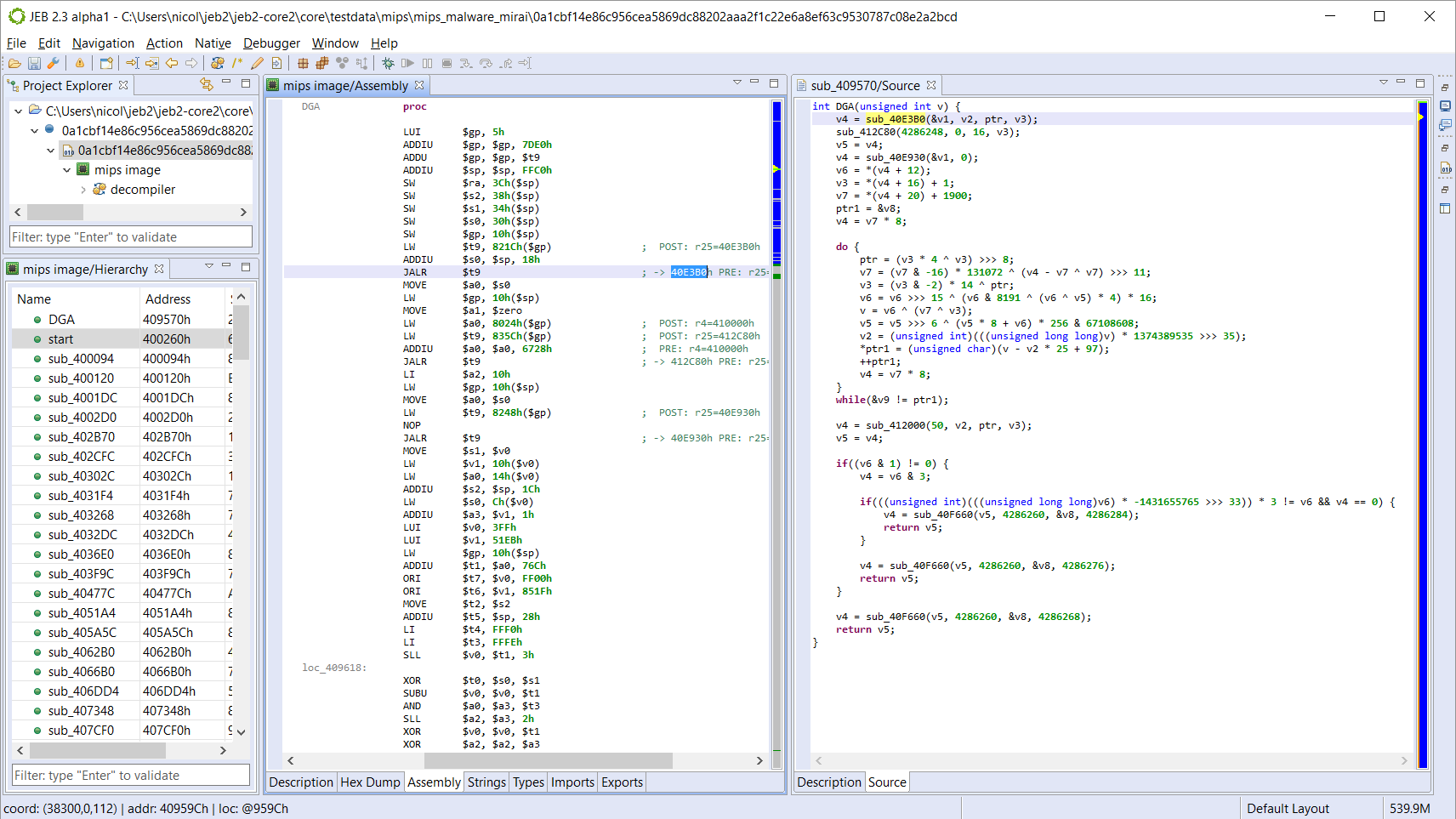
MIPS Decompiler
Use JEB to reverse engineer MIPS embedded programs and malware.
Our MIPS processor and microcontroller machine code decompiler allows reverse engineers and security auditors to analyze malicious MIPS programs and audit complex embedded systems (routers, set-top boxes, IOT devices, etc.).
The MIPS decompiler provides the following features:
- Augmented disassembly including resolution of dynamic callsites and syscalls, candidate values determination for registers, dynamic cross-references, etc.
- Decompilation of MIPS 32-bit to pseudo-C source code.
- Advanced optimization passes to thwart protected or obfuscated code.
- Interactive layer allowing refactoring: type definition, stackframe building, renaming/commenting/cross-referencing, etc.
- Full API to perform advanced and/or automated code analysis in Python or Java.
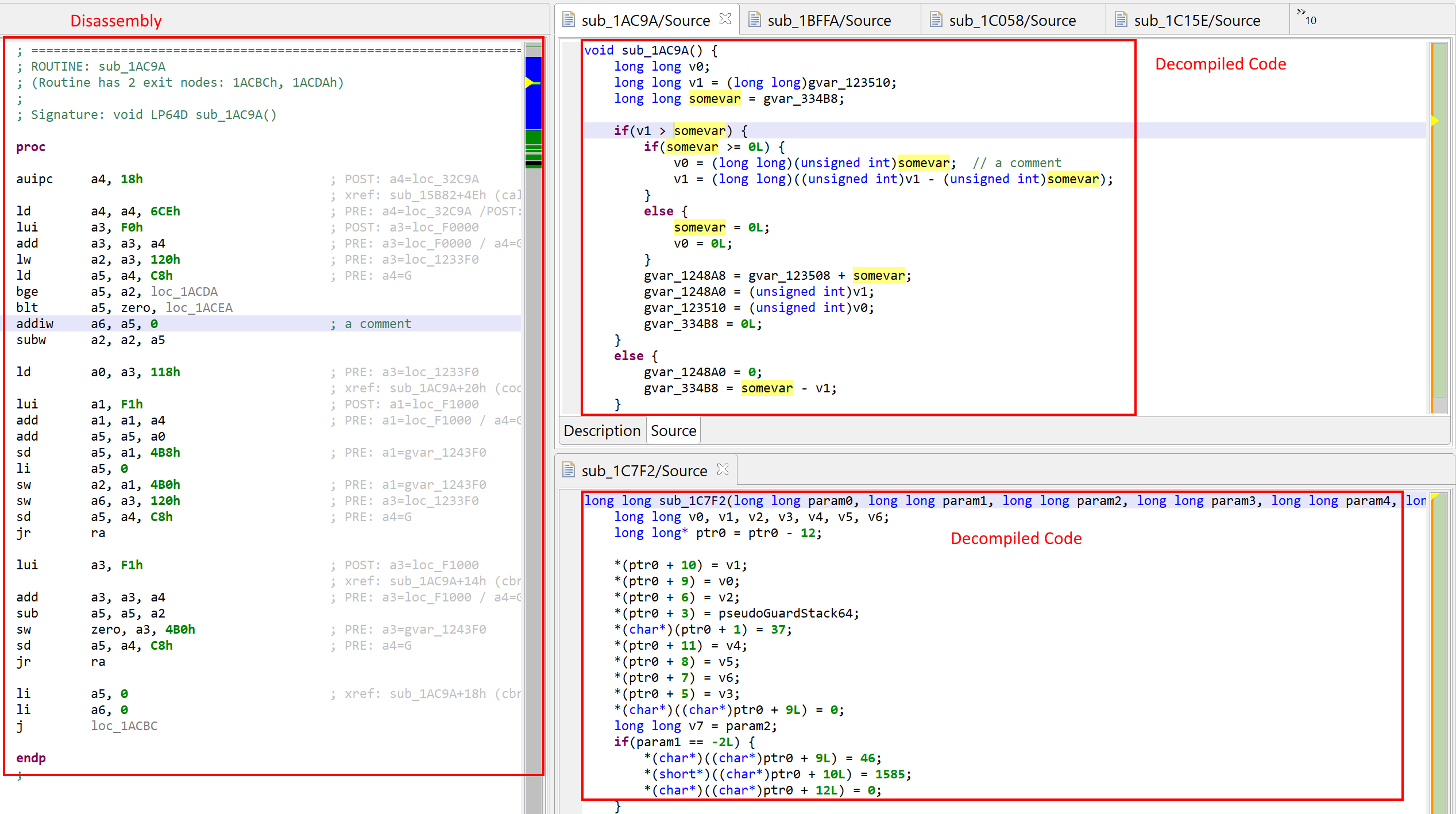
RISC-V Decompiler
Use the JEB RISC-V modules to reverse engineer RV32/RV64 programs and binaries.
Our RISC-V machine code decompiler allows reverse engineers and security auditors to analyze RV32 and RV64 programs.
Features specific to the RISC-V plugins:
- Code object files: support RISC-V in Linux ELF, Windows PE, or headless code (e.g. firmware).
- Disassembler: support for RV32/RV64, regular and compressed opcodes for the following ISA extensions: I (integer), Zifencei, Zicsr, M (multiply), A (atomic), F (single-float), D (double-float), C (compressed). Note that RV128, RVE (embedded) and other more "exotic" extensions (mem tx, simd, vectors, etc.) are currently not supported.
- Decompilation: support for RVI (decompilation of the integer/general-purpose operations) for 32-bit and 64-bit. Decompiler support for F/D extensions (floating-point instructions) is a planned addition.
- Relocations: support for common ELF relocations specific to RISC-V. Common PLT resolver stubs are handled.
- Calling conventions: calling conventions ILP32D and LP64D are supported. Custom calling conventions can be defined.
- Type libraries: ARM or MIPS type libraries for Linux 32/64 or Windows 32/64 can be reused.
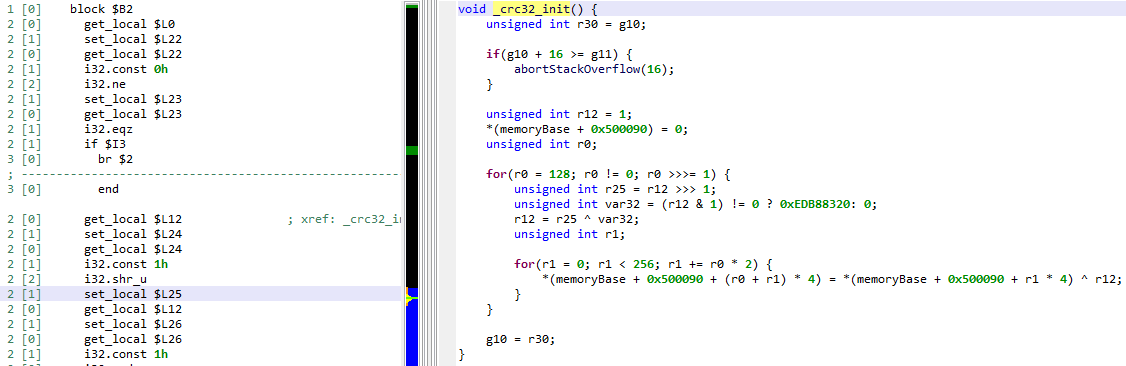
WebAssembly Decompiler
Use JEB to reverse engineer WebAssembly binary modules.
The WebAssembly plugins provide the following features:
- Augmented disassembly and parsing of wasm binary modules.
- Decompilation of wasm bytecode to pseudo-C source code.
- Advanced optimization passes to thwart protected or obfuscated code.
- Interactive layer for typing/renaming/commenting/cross-referencing, etc.
- Full API access for scripting and plugins.
JEB WebAssembly plugins can also be used to decompile Smart Contracts compiled to wasm, such as EOS or Parity contracts.
Read our technical paper "Reverse Engineering WebAssembly"
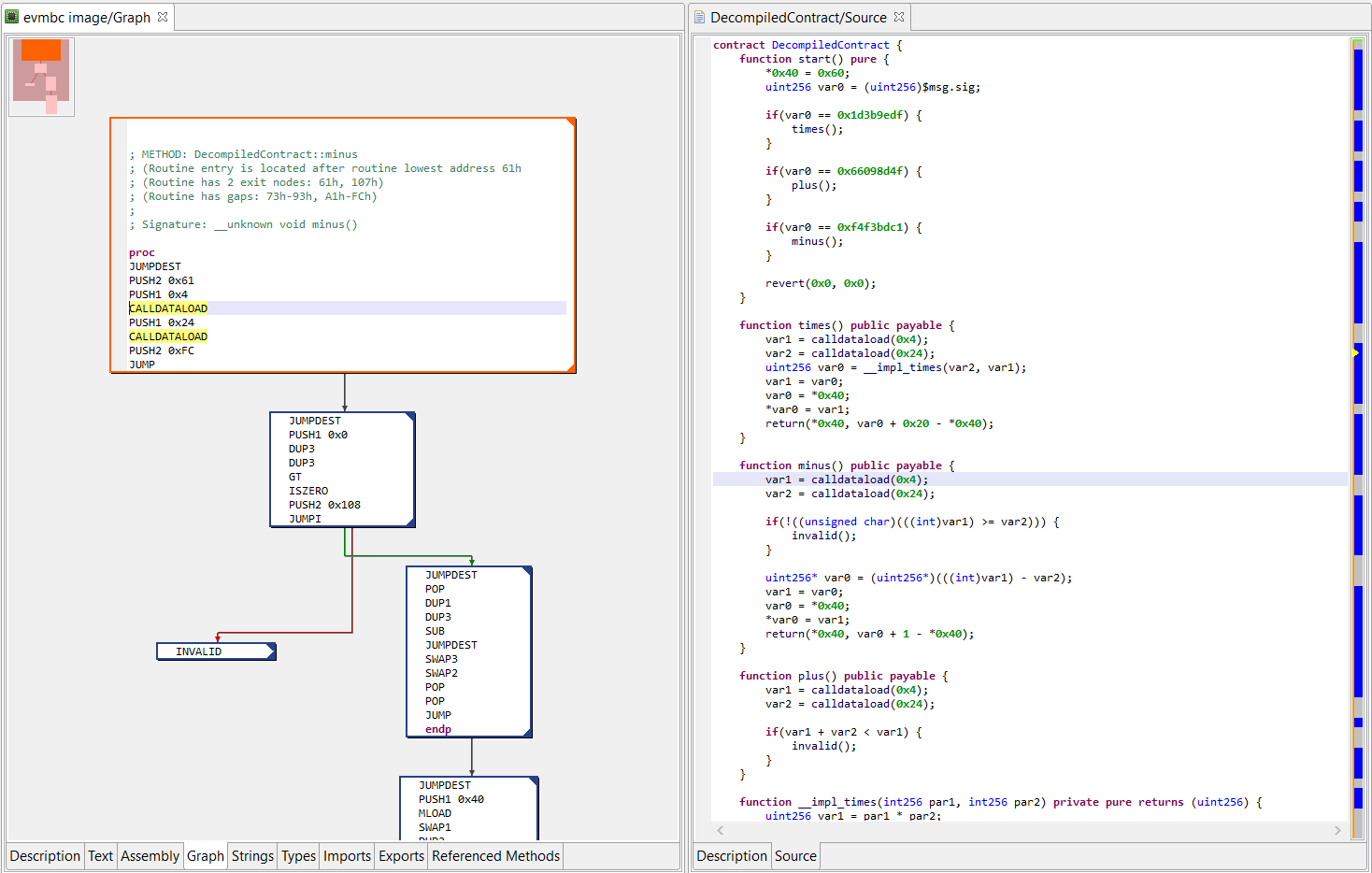
Ethereum Decompiler
Use JEB to reverse engineer Ethereum opaque smart contracts and dApps to Solidity-like high-level code.
Cut down on costly reverse engineering time: decompile Ethereum smart contracts to
Solidity-like source code to easily understand and review closed-source contracts and dApps.
- Decompile EVM contract code to Solidity-like high-level code using our Ethereum decompiler.
- Annotate the analysis results to better understand what the compiled contract or dApp is doing.
- Automate or script your reverse engineering tasks via our API.
The picture on the right-side shows JEB dual-pane "EVM assembly/decompiled code" view of a contract live on Ethereum's mainnet. (Click to enlarge.)
Simatic S7 PLC Program Decompiler
The S7 PLC block decompiler extension provides support for reverse engineers and security auditors to analyze Siemens Simatic S7 PLC programs. Click the button below for full details.
PDF Document Analyzer
Analyze malicious Adobe™ PDF files using the best PDF document analyzer in the industry.
Our PDF module breaks down and decodes PDF files to provide access to its inner components such as resources and scripts. It detect structure corruptions and issues notifications to report suspicious areas. Leverage the PDF module either through the desktop client or a headless client, such as a file analyzer stack or automation pipeline.
Use our PDF analyzer to manually or automatically reverse engineer documents of all sizes.
- Break-down the PDF structure into a visually compelling and navigable tree.
- Deal with corrupt files, complex streams (eg, multiple encodings, etc.).
- Retrieve 20+ notifications and alerts generated by the analyzer to pin-point suspicious areas and use them to issue a determination on the file.
- Extract embedded Javascript even in the most extreme cases.
- Automate the reverse engineering process via the JEB API to perform bulk analysis.
Features Matrix
This table presents which analysis modules and core features ship with our various license types.
| Build Type > | Community Edition |
(or Pro Floating) |
|
|---|---|---|---|
| Base | |||
| Suitable for enterprise or professional use | |||
| Decompilers | |||
| Dalvik Decompiler (a.k.a. Android Decompiler) | |||
| Deobfuscation module for "virtualized" code (details) | |||
| Advanced deobfuscators requiring native code emulation (JNI) (details, details) | |||
| Generic APK unpacker plugin (attempt to collect dyn. dex files) (details) | |||
| Java Decompiler | |||
| Intel x86 Decompiler | |||
| Intel x86-64 Decompiler | |||
| ARM Decompiler | |||
| ARM64 Decompiler | |||
| MIPS Decompiler | |||
| MIPS64 Decompiler | |||
| RISC-V Decompiler | |||
| S7 PLC Block Decompiler | |||
| WebAssembly Decompiler | |||
| Ethereum Decompiler for Smart Contracts (EVM Decompiler) | |||
| Diem (Libra) Decompiler for Move modules (open-sourced) | |||
| Base Plugins | |||
| Archive files (zip, 7z, tar) | |||
| Image files (bmp, png, jpg, gif, ico) | |||
| Structured text files (html, xml, json) | |||
| Certificate files (x.509) | |||
| Application Processors | |||
| Android APK (incl. dex, odex, x-apk) | |||
| Windows PE/PE64/COFF, PDB | |||
| Linux ELF/ELF64 | |||
| Mach-O, Mach-O/FAT | |||
| Intel HEX (ihex) | |||
| Chrome Extension (crx) | |||
| WebAssembly module (wasm) | |||
| Ethereum contracts (evm) | |||
| Disassemblers | |||
| Dalvik Disassembler | |||
| Intel x86 Disassembler | |||
| Intel x86-64 (AMD64) Disassembler | |||
| ARM (32, Thumb) Disassembler | |||
| ARM64 (Aarch64) Disassembler | |||
| MIPS Disassembler | |||
| RISC-V Disassembler | |||
| Atmel AVR 8-bit Disassembler | |||
| Miscellaneous Binary Parser Plugins | |||
| Flutter/Dart AOT Snapshot Parser (limitations) | |||
| Debuggers | |||
| Dalvik Debugger (Android) | |||
| Intel x86 Debugger (GDB/LLDB all platforms, incl. Android) | |||
| Intel x86-64 Debugger (GDB/LLDB all platforms, incl. Android) | |||
| ARM Debugger (GDB/LLDB all platforms, incl. Android) | |||
| ARM64 Debugger (GDB/LLDB all platforms, incl. Android) | |||
| MIPS Debugger (GDB/LLDB all platforms, incl. Android) | |||
| Document Parsers | |||
| Adobe PDF | |||
| FAT file systems (file access table) | (plugin) | ||
| Platform | |||
| Persist JEB Projects to JDB2 Databases | |||
| Interactivity (refactoring, renaming, commenting, etc.) | |||
| Graphing (CFG, Callgraphs, etc.) | |||
| Support for multiple Artifacts in a same Project | |||
| Extensions - Client scripts in Python | |||
| Extensions - Back-end plugins in Java | |||
| Automation / headless launcher | |||
| Work offline |