Update (2025/09/10): The legacy assistant is superseded by VIBRE, a full-blown conversational AI agent available in JEB 5.32+. Read more here!
Update (2025/08/17): The assistant was updated for the release of JEB 5.31. Restrictions in terms of decompiled code size were loosened; back-end language models were upgraded to provide better suggestions.
Update (2023/12/06): Several restrictions are lifted in JEB 5.6 to make the Assistant available for Java decompiled output generated by dexdec (it is currently limited to C output generated by gendec).
Starting from JEB 5.2, you may use the experimental “JEB Assistant” to infer names for decompiled classes, fields, methods and method parameters.
Below is a decompiled aarch64 routine found in the BPFDoor malware. A raw decompilation does not produce any useful name (the default routine name is sub_40157C).
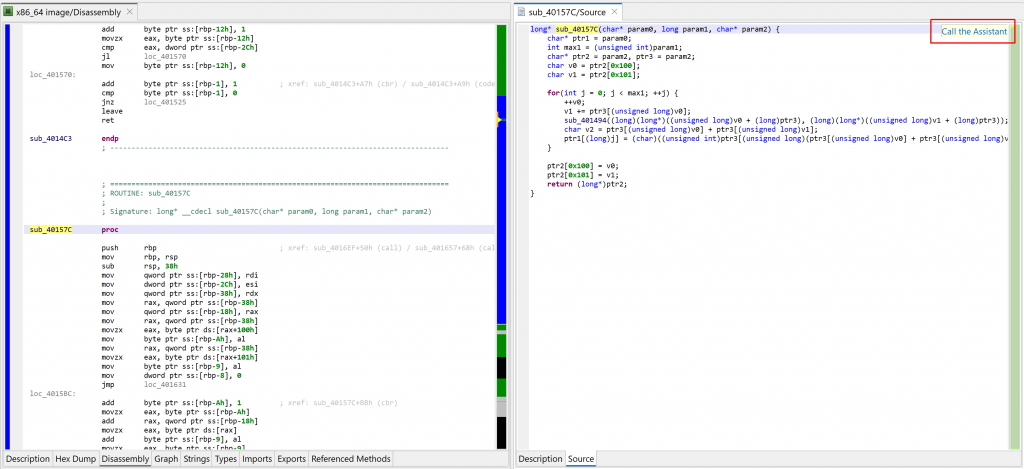
You may click the “Call the Assistant” button (also available via the Action menu, Request Assistant handler, or the back-tick keyboard shortcut) to query the assistant via JEB.IO. At the time of writing, a JEB.IO account is not required to access the assistant.
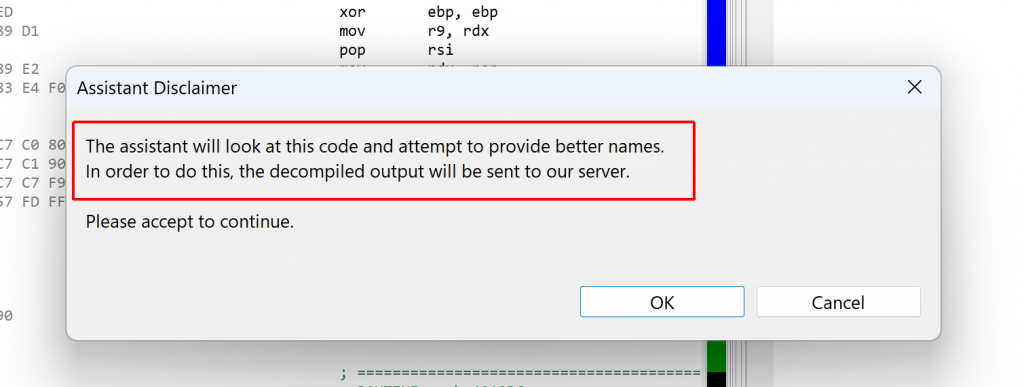
Upon first request, a disclaimer will be shown, letting you know that the decompiled code must be sent to our server:
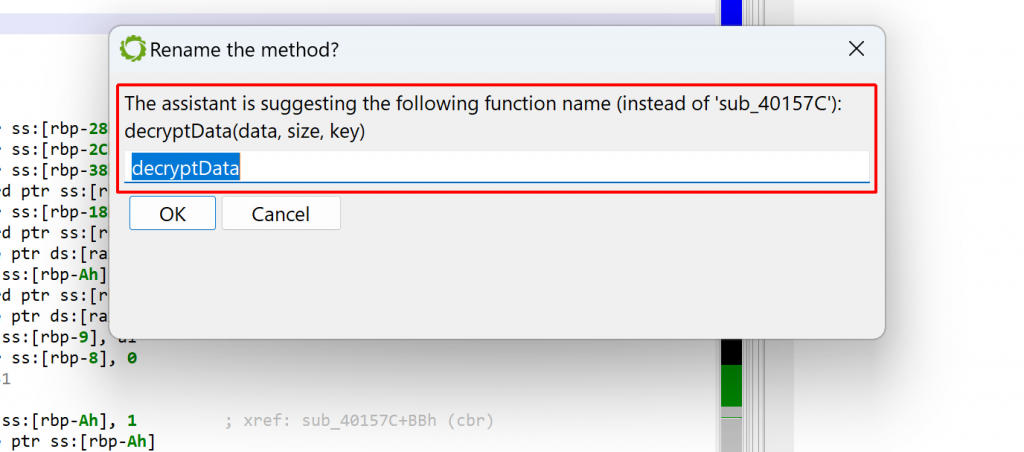
The assistant may return a better name for the method and its parameters. Sometimes, the names may be incorrect, yet provide some insight into what the method is doing. Other times, they may be entirely out of scope! It is always better to take the provided results as hints, rather than absolute truths.
In the case of our mysterious method, the assistant did provide valuable information: decryptData(data, size, key). Indeed, the method is a decryption function — more specifically, rc4 with a pre-computed sbox. The parameter names are (almost) correct.
You may decide to apply the suggested method name directly. The suggested parameter names are not applied automatically.
Currently, some limitations apply:
- The assistant is not available via the JEB API and requests are rate-limited (at most one every 5 seconds).
- The suggestions are mostly for class, method, and field names. Sometimes, suggestions for variable names are returned as well, but won’t be auto-applied.
A JEB.IO account is not required at this time to use the assistant! Anybody can use it to (sometimes) gain insight into obscure decompilations. We hope it will help you in your reverse-engineering efforts. Please let us know your feedback through the usual channels (email, Slack, etc.).
Until next time 🙂 — Nicolas.